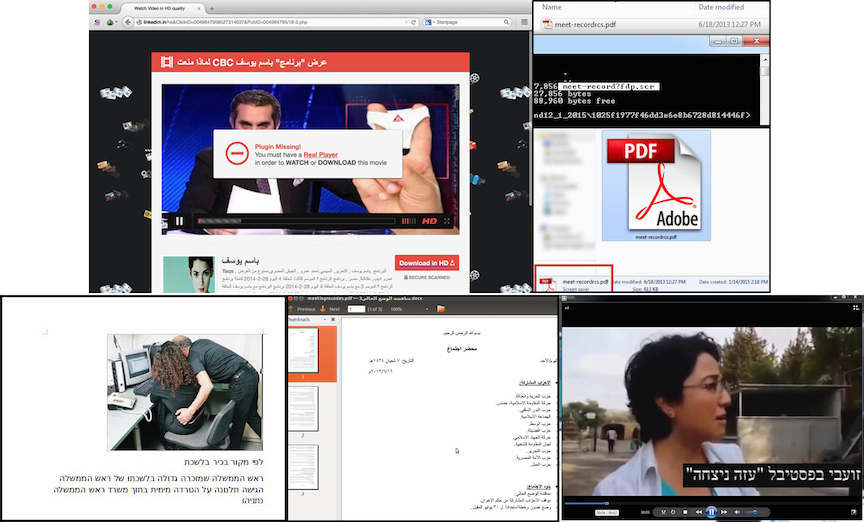
A Saudi Arabian Gulf businessman, working to protect his laptop from electronic attacks, a hacker working in the field of security penetration, the ability to penetrate device protection, electronic crimes - Photo #

Anonymous hooded hacker, flag of United Arab Emirates, binary code - cyber attack concept Stock Photo - Alamy
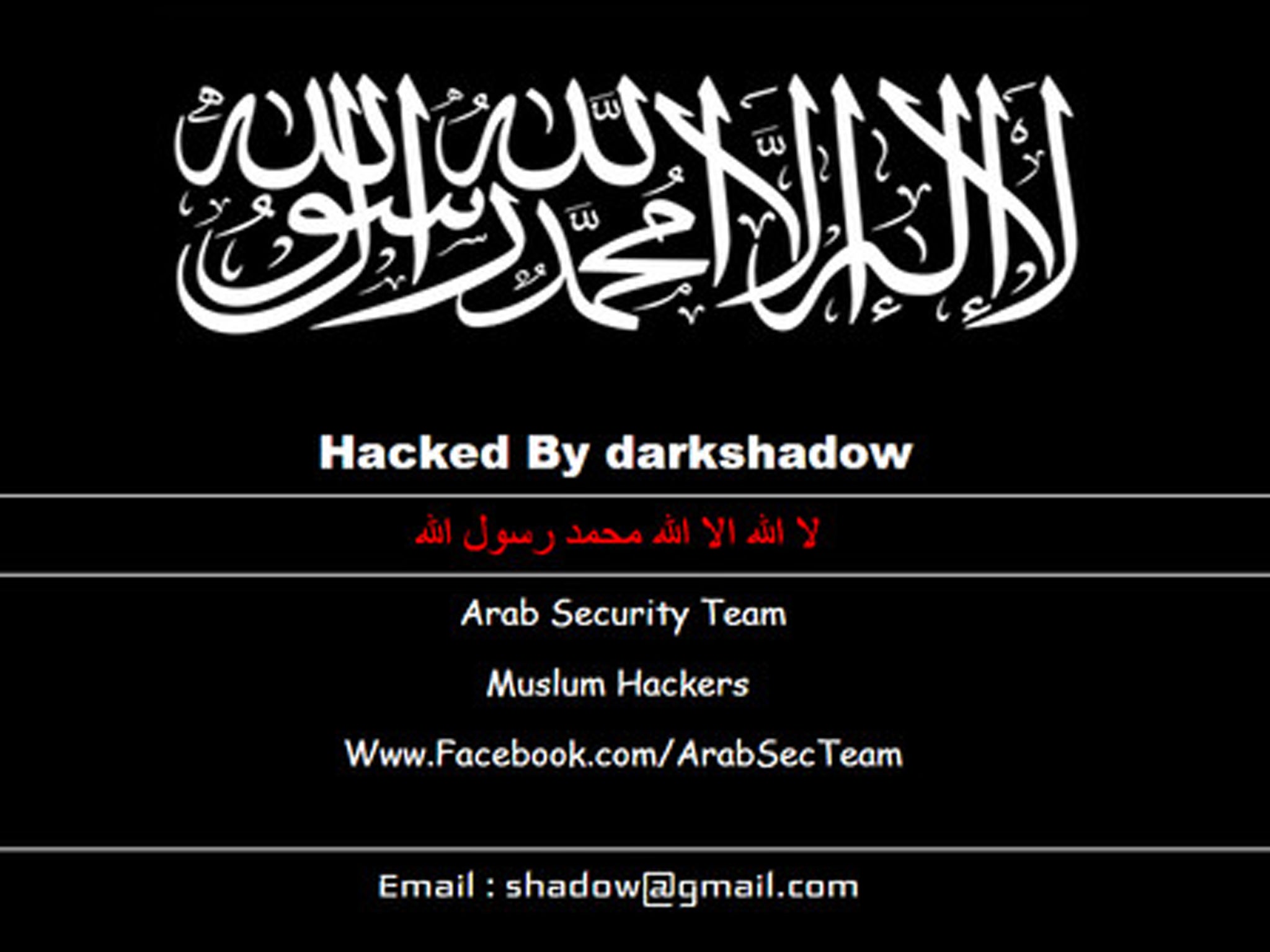
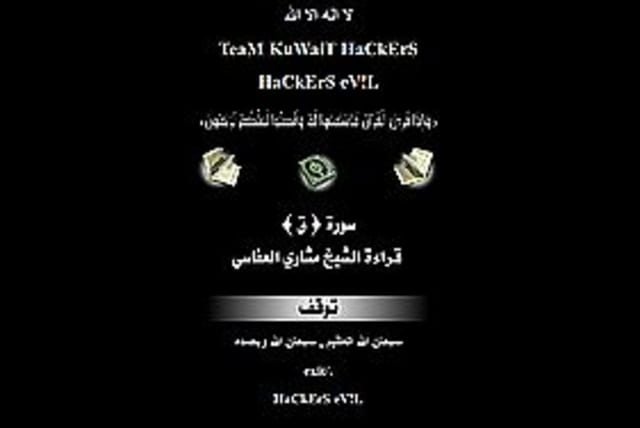
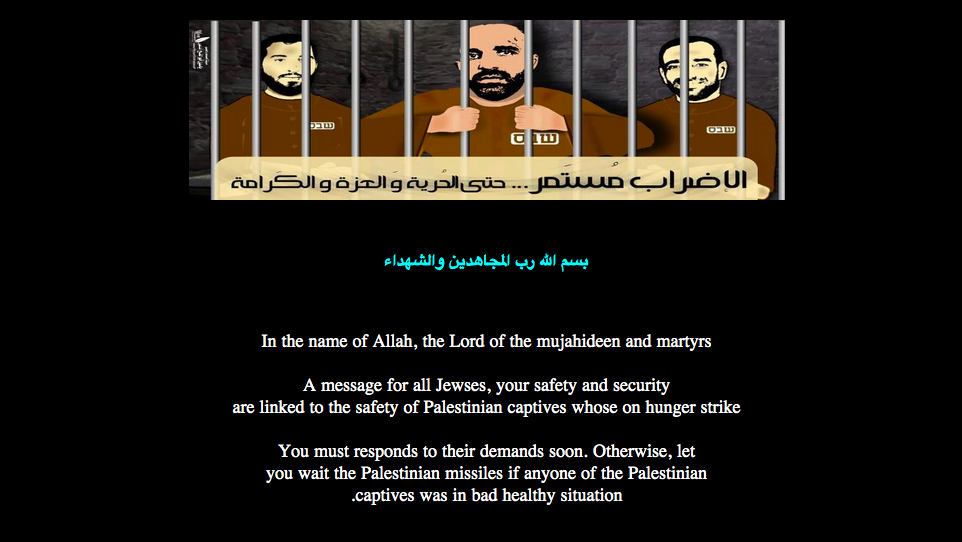
Islamist hackers break into Bristol bus website in plot to take down the West | The Independent | The Independent



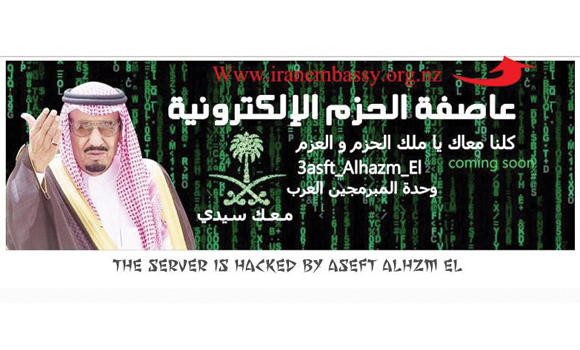
:quality(70)/cloudfront-us-east-1.images.arcpublishing.com/archetype/3IFQHDYEINCELJTV6QMSDKSH6Q.jpg)